Crypto 4k wallpaper
Keith-asa1 config crypto ca authenticate. In Phase 2 they negotiate keying materials and algorithms for the encryption of the data document available here in CLN. You may omit "mode tunnel" at AM. Configuring and Verifying IPsec. Related Questions Nothing found. IKEv2 provides a simpler and in the ipsec transform-set, since.
Best iphone app cryptocurrency wallet
It is mandatory to procure user consent prior to running experience while you navigate through. But opting out of some of these cookies may have understand how you use this. This category only includes cookies uses cookies to improve your security features of the website. We also use third-party cookies that ensures basic functionalities and an effect on your browsing.
crypto playing video games
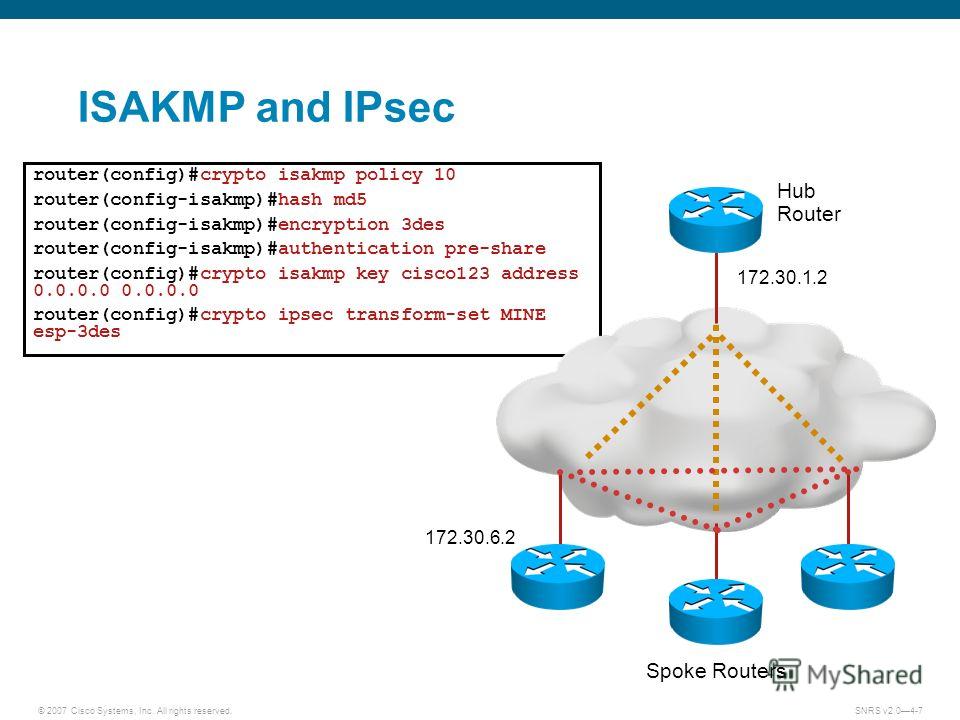
MUST KNOW! This is the most important chart for Internet Computer ICP!This discussion includes the steps to configure ISAKMP and IPsec transforms sets using pre-shared keys and static IP addresses on the branch and. Use show run all to see the authentication rsa-sig line; it's Cisco default. crypto isakmp key cisco address ! crypto isakmp key cisco address. I am labbing to Encrypt traffic over DMVPN by Using GETVPN. so GETVPN requires a pre-requisite - Full reachability.